A risk actor quietly spent the final two years integrating themself within the core workforce of maintainers of XZ Utils, a free software program command-line knowledge compressor extensively utilized in Linux programs. The attacker slowly managed to combine a backdoor within the software program that was designed to intrude with SSHD and permit distant code execution by way of an SSH login certificates. The backdoor was found a couple of days earlier than being launched on a number of Linux programs worldwide.
The risk actor is suspected to be a developer with or utilizing the title Jian Tan. A number of safety consultants consider this provide chain assault is likely to be state sponsored.
What’s XZ Utils, and what’s the XZ backdoor?
XZ Utils and its underlying library liblzma is a free software program instrument that implements each XZ and LZMA, that are two compression/decompression algorithms extensively utilized in Unix-based programs, together with Linux programs. XZ Utils is utilized by many operations on these programs for compressing and decompressing knowledge.
The CVE-2024-3094 backdoor present in XZ Utils was carried out to intrude with authentication in SSHD, the OpenSSH server software program that handles SSH connections. The backdoor enabled an attacker to execute distant code by way of an SSH login certificates. Solely XZ Utils variations 5.6.0 and 5.6.1 are impacted.
How the XZ backdoor was carried out cautiously for greater than years
On March 29, 2024, Microsoft software program engineer Andres Freund reported the invention of the backdoor. He discovered it when he turned fascinated about odd conduct of a Debian sid set up, resembling SSH logins taking a number of CPU and Valgrind errors and determined to research the signs in depth. Freund defined that the invention of the backdoor in XZ was luck, because it “actually required a number of coincidences.”
But it seems that the implementation of the backdoor has been a really quiet course of that took about two years. In 2021, a developer named Jian Tan, username JiaT75, appeared out of the blue to begin engaged on the XZ Utils code, which isn’t uncommon as a result of builders of free software program usually work collectively on updating code. Tan contributed steadily to the XZ challenge since late 2021, slowly constructing belief locally.
In Might 2022, an unknown consumer utilizing the faux title Dennis Ens complained on the XZ mailing record that the software program replace was not satisfying. One other unknown consumer, Jigar Kumar, got here into the dialogue two instances to strain the primary developer of XZ Utils, Lasse Collin, so as to add a maintainer to the challenge. “Progress won’t occur till there may be new maintainer,” Jigar Kumar wrote. “Why wait till 5.4.0 to vary maintainer? Why delay what your repo wants?”
In the meantime, Collin expressed that “Jia Tan has helped me off-list with XZ Utils and he may need an even bigger function sooner or later at the very least with XZ Utils. It’s clear that my sources are too restricted (thus the various emails ready for replies) so one thing has to vary in the long run.” (Collin wrote Jia in his message whereas different messages reference Jian. So as to add to the confusion, Jian’s nickname is JiaT75.)
Within the months that adopted, Tan turned more and more concerned in XZ Utils and have become co-maintainer of the challenge. In February 2024, Tan issued commits for variations 5.6.0 and 5.6.1 of XZ Utils, each of which contained the backdoor.
It’s also fascinating to notice that in July 2023, Tan requested to disable ifunc (GNU oblique operate) on oss-fuzz, a public instrument made to detect software program vulnerabilities. That operation was most likely finished to permit the backdoor in XZ to remain undetected as soon as it was launched, because the backdoor makes use of that operate to realize its targets.
Lastly, a number of individuals accountable for completely different Linux distributions have been contacted by the attacker to incorporate the backdoored variations of XZ Utils in their very own distributions. Richard WM Jones from RedHat wrote about it on a discussion board: “Very annoying – the obvious creator of the backdoor was in communication with me over a number of weeks making an attempt to get xz 5.6.x added to Fedora 40 & 41 due to it’s ‘nice new options’. We even labored with him to repair the valgrind difficulty (which it seems now was attributable to the backdoor he had added). We needed to race final evening to repair the issue after an inadvertent break of the embargo. He has been a part of the xz challenge for two years, including all types of binary take a look at recordsdata, and to be sincere with this stage of sophistication I might be suspicious of even older variations of xz till confirmed in any other case”. Tan additionally tried to have it included in Ubuntu.
XZ backdoor: A extremely technical assault
Along with the extremely elaborated social engineering lined beforehand on this article, the backdoor itself could be very advanced.
Microsoft’s senior risk researcher Thomas Roccia designed and published an infographic to point out the entire operation resulting in CVE-2024-3094 (Determine A).
Determine A
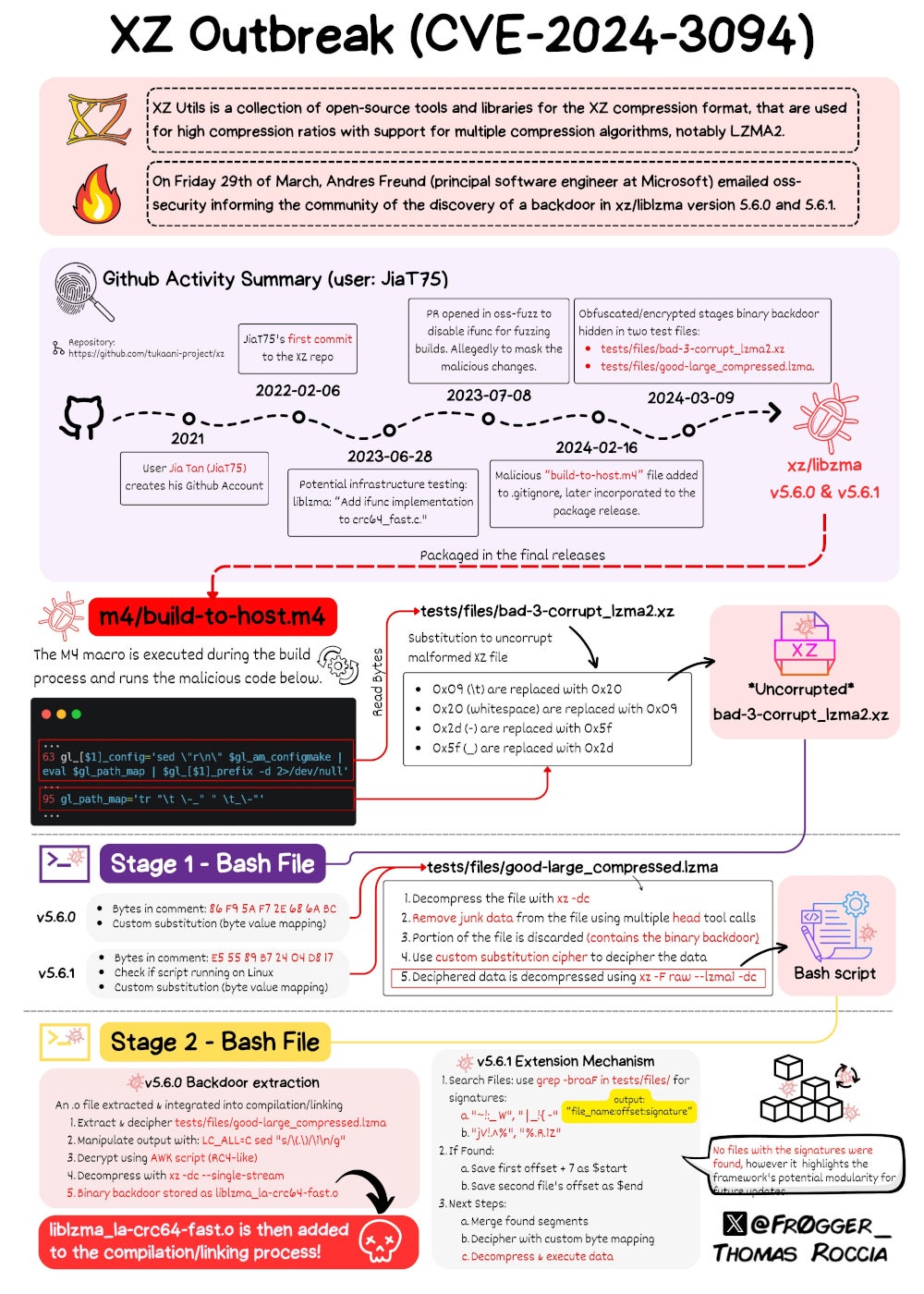
The backdoor consists of a number of elements which have been included over a number of commits on the XZ Utils GitHub, described in depth by Freund.
Gynvael Coldwind, managing director of HexArcana Cybersecurity GmbH,a cybersecurity firm offering consulting and programs companies, wrote in an in depth evaluation of the backdoor that “somebody put a number of effort for this to be fairly harmless wanting and decently hidden. From binary take a look at recordsdata used to retailer payload, to file carving, substitution ciphers, and an RC4 variant carried out in AWK all finished with simply normal command line instruments. And all this in 3 phases of execution, and with an ‘extension’ system to future-proof issues and never have to vary the binary take a look at recordsdata once more.”
DOWNLOAD: Open supply fast glossary from TechRepublic Premium
Martin Zugec, technical options director at Bitdefender, stated in an announcement offered to TechRepublic that “this seems to be a meticulously deliberate, multi-year assault, presumably backed by a state actor. Contemplating the large efforts invested and the low prevalence of susceptible programs we’re seeing, the risk actors accountable have to be extraordinarily sad proper now that their new weapon was found earlier than it could possibly be extensively deployed.”
Which working programs are impacted by the XZ backdoor?
Because of Freund’s discovery, the assault was stopped earlier than being unfold on a wider scale. The cybersecurity firm Tenable uncovered the next working programs identified to be affected by the XZ backdoor:
- Fedora Rawhide.
- Fedora 40 Beta.
- Fedora 41.
- Debian testing, unstable and experimental distributions variations 5.5.1alpha-01 to five.6.1-1.
- openSUSE Tumbleweed.
- openSUSE MicroOS.
- Kali Linux.
- Arch Linux.
In a weblog publish, Purple Hat reported that no variations of Purple Hat Enterprise Linux are affected by CVE-2024-3094.
Debian indicated that no secure model of the distribution are affected, and Ubuntu posted that no launched variations of Ubuntu have been affected.
MacOS homebrew package deal supervisor reverted XZ from 5.6.x to five.4.6, an older but secure model. Bo Anderson, maintainer and Homebrew technical steering committee member, declared that Homebrew doesn’t “… consider Homebrew’s builds have been compromised (the backdoor solely utilized to deb and rpm builds) however 5.6.x is being handled as now not reliable and as a precaution we’re forcing downgrades to five.4.6.”
Learn how to mitigate and shield from this XZ backdoor risk
Extra programs is likely to be affected, particularly these on which builders compiled the susceptible variations of XZ. Safety firm Binarly gives a web based detection instrument that could possibly be used to check programs to see if they’re affected by the XZ backdoor.
The model of XZ ought to be rigorously checked, as variations 5.6.0 and 5.6.1 include the backdoor. It’s suggested to revert to a earlier identified secure model of XZ Utils, resembling 5.4.
Software program provide chain assaults are rising
As beforehand reported on TechRepublic, software program provide chain assaults are more and more being utilized by risk actors.
But common software program provide chain assaults principally encompass managing to compromise a key account within the means of the event of software program, and use the account to push malicious content material to professional software program, which frequently will get detected fairly quickly. Within the XZ Utils case, it is extremely completely different as a result of the risk actor rigorously managed to realize the belief of professional builders and grow to be one of many maintainers of the instrument, permitting him to slowly push completely different susceptible elements of code into the software program with out being seen.
Software program provide chain assaults should not the one rising threats; different provide chain assaults primarily based on IT merchandise are additionally rising.
Due to this fact, firms ought to be certain that third events are considered of their assault floor monitoring.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.


/cdn.vox-cdn.com/uploads/chorus_asset/file/25338407/3_Body_Problem_n_S1_E3_00_34_33_04RC.jpg_3_Body_Problem_n_S1_E3_00_34_33_04RC.jpg)



