Intel has revealed a number of obvious shortcoming in among the safety protections provided by its nice rival AMD.
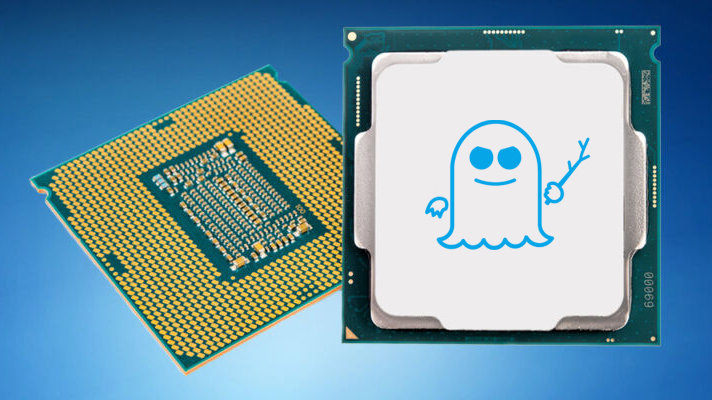
The corporate had just lately found new Spectre-like vulnerabilities affecting each its chips, in addition to these produced by ARM. AMD’s gadgets have been reportedly immune, however whereas Intel was investigating its rival’s earlier patches to attempt to discover a method to mitigate the brand new flaws, it discovered them to be damaged.
AMD was instantly notified, and the corporate rapidly pushed a brand new safety bulletin, updating its steering, and recommending an alternate resolution to the Spectre downside.
AMD issued the flawed resolution again in 2018, and now it might appear that just about each fashionable AMD processor, together with Ryzen and EPYC households, is affected.
No recognized exploits
In its safety bulletin, AMD acknowledges the issue, however provides that there is no such thing as a proof of the flaw being abused on any endpoints within the wild.
Final week, information broke of a brand new variant of the dreaded Spectre vulnerability being found, albeit in a proof-of-concept. Nevertheless, the sheer promise of its harmful energy prompted all main chipmakers into motion.
Researchers from Intel and VUSec found the flaw in each Intel and ARM gadgets, and have dubbed it Department Historical past Injection (BHI).
It bypasses Intel’s eIBRS, in addition to Arm’s CSV2 mitigations, enabling cross-privilege Spectre-v2 exploits, and kernel-to-kernel exploits. It additionally permits menace actors to inject predictor entries into the worldwide department prediction historical past, primarily leaking delicate knowledge, resembling passwords.
The checklist of affected chips is kind of intensive, overlaying all of Intel’s processors, from Haswell (2013) onwards (to Ice Lake-SP and Alder Lake) are reportedly affected, in addition to varied ARM chips (Cortex A15, A57, A72, Neoverse V1, N1, N2).
Fortuitously, that is additionally only a proof-of-concept vulnerability that’s already being mitigated by each firms, which implies its use on laptops or computer systems within the wild ought to be comparatively restricted. Nevertheless, earlier fixes all affected the efficiency of the chips, an issue that may rear its ugly head, as soon as once more.
Spectre, together with Meltdown, are two extraordinarily extreme {hardware} vulnerabilities that have an effect on Intel, IBM POWER, and a few ARM-based processors. Whereas Intel has since applied {hardware} mitigations for the vulnerability in newer processors, older ones should depend on software program fixes that include a efficiency penalty.
An in depth breakdown of the vulnerability, and its exploit (which appears to be comparatively extra complicated than its early-days predecessor), may be discovered on this hyperlink.
By way of: Tom’s {Hardware}




/cdn.vox-cdn.com/uploads/chorus_asset/file/25452998/MSI_Claw_Verge_Sean_Hollister_1_10.jpg)

