Apple’s iOS 14 working system features a new safety sandbox system designed to guard Messages customers from probably malicious code, in keeping with new analysis shared on Thursday.
Found by Samuel Groß, a member of Google’s Undertaking Zero workforce, the brand new sandbox is called BlastDoor and is restricted to the Messages stage of iOS, experiences ZDNet.
BlastDoor quietly shipped with iOS 14 final yr, although Apple has not publicly referenced the safety function. Groß detailed the “tightly sandboxed” service in a weblog put up at this time.
Written within the comparatively protected Swift programming language, BlastDoor is liable for parsing almost all untrusted knowledge in Messages, Groß says. Previous to iOS 14, steps like decompressing binary knowledge, decoding the plist from a binary serialization format, subject extraction, and decoding of the “x” key had been all carried out by imagent. Now, imagent is on the head of the processing movement, however important operations are forwarded to BlastDoor.
In line with Groß, the sandbox prohibits communication with most IPC companies, blocks almost all file system interplay, forbids any interplay with IOKit drivers and denies outbound community visitors. Primarily, the system unpacks content material — each textual content and attachments — in a protected atmosphere and prevents malicious code from interacting with iOS or accessing native knowledge.
“General, these modifications are in all probability very near one of the best that might’ve been accomplished given the necessity for backwards compatibility, and they need to have a big affect on the safety of iMessage and the platform as an entire,” Groß writes, noting that Messages in iOS 14 additionally permits for resliding of the shared cache and exponential throttling. “It is nice to see Apple placing apart the assets for these sorts of huge refactorings to enhance finish customers’ safety.”
The safety researcher was tipped off to the brand new safety protocol after studying a report from College of Toronto’s Citizen Lab that detailed a Messages vulnerability leveraged to infiltrate and spy on journalists’ iPhones. Referred to as “Kismet,” the exploit was in circulation for at the least a yr earlier than being neutralized with the discharge of iOS 14.
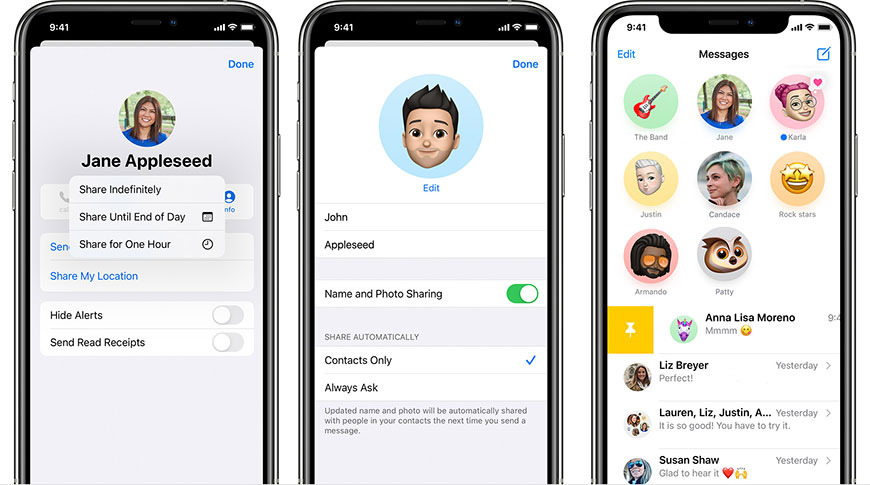
Together with safety enhancements, Apple launched quite a few user-facing options to Messages in its newest cellular OS together with pinned conversations, chat threads, and inline mentions.