What You Ought to Know:
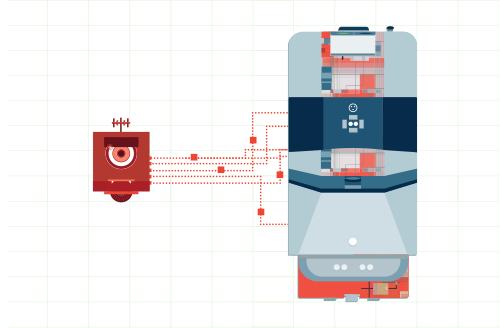
– Cynerio, a supplier of healthcare IoT safety options, introduced the invention, exploitation, and disclosure of 5 zero-day vulnerabilities collectively referred to as JekyllBot:5, that have an effect on generally used robots present in tons of of hospitals worldwide.
– Vulnerabilities present in Aethon Tug hospital robots may enable attackers to avoid safety and remotely surveil and work together with sufferers, hinder remedy distribution, and disrupt day-to-day hospital operations.
JekyllBot:5 Vulnerabilities for Aethon TUG Autonomous Robots
Aethon TUG sensible autonomous robots are designed to deal with healthcare-related duties corresponding to distributing remedy, cleansing, and transporting hospital provides. The robots leverage radio waves, sensors, cameras and different know-how to open doorways, take elevators and journey all through hospitals unassisted with out bumping into folks and objects. Nevertheless, the know-how that allows the robots to independently transfer across the hospital are what make their vulnerabilities so harmful within the palms of a possible attacker.
The JekyllBot:5 vulnerabilities have been found by the Cynerio Reside analysis group and reside within the TUG Homebase Server’s JavaScript and API implementation, in addition to a WebSocket that relied on absolute belief between the server and the robots to relay instructions to them. A few of the extra extreme assault eventualities in danger by probably exploiting these vulnerabilities, which ranked as excessive as a 9.8 CVE rating, embody:
– Disrupting or impeding the well timed supply of affected person medicines and lab samples important for optimum affected person care
– Interfering with important or time-sensitive affected person care and operations by shutting down or obstructing hospital elevators and door locking programs
– Monitoring or taking movies and footage of weak sufferers, employees, and hospital interiors, in addition to delicate affected person medical information
– Controlling all bodily capabilities and places of the robots to permit entry to restricted areas, interplay with sufferers or crashing into employees, guests and gear
– Hijacking reputable administrative consumer periods within the robots’ on-line portal and injecting malware via their browser to perpetrate additional cyberattacks on IT and safety group members at healthcare amenities.
Mitigation Particulars
The JekyllBot:5 vulnerabilities have been mitigated by the system producer following Cynerio’s disclosure of the dangers via the CISA Coordinated Vulnerability Disclosure course of. A number of patches have been utilized to the robotic fleets at every Aethon buyer hospital, together with one main patch that required changing firmware and an working system replace for robots at some hospitals. As well as, Aethon was in a position to replace the firewalls at specific hospitals recognized to have weak robots in order that public entry to the robots via the hospitals’ IP addresses was prevented because the fixes have been rolled out.
“These zero-day vulnerabilities required a really low talent set for exploitation, no particular privileges, and no consumer interplay to be efficiently leveraged in an assault, “ mentioned Asher Brass, lead researcher on the JekyllBot:5 vulnerabilities and Head of Cyber Community Evaluation at Cynerio. “If attackers have been in a position to exploit JekyllBot:5, they might have utterly taken over system management, gained entry to real-time digital camera feeds and system information, and wreaked havoc and destruction at hospitals utilizing the robots.”