What simply occurred? Researchers with Guardio Safety uncovered a “huge marketing campaign” of malicious data-collecting browser extensions. The analysts dubbed it “Dormant Colours” due to the malware’s deal with colour and magnificence themes — Motion Colours, Energy Colours, Tremendous Colours, and so forth. Dormant Colours consists of 30 completely different extensions that thousands and thousands of customers have downloaded.
The seemingly innocent “helpers” promote themselves as webpage modifiers, permitting customers to vary issues like background colours and font types on webpages they go to. Nevertheless, underneath the hood, they’ve a number of malicious endeavors, together with hijacking your search/shopping histories, inserting commercials inside visited pages, and side-loading malicious code with out being detected.
The result’s a community of contaminated computer systems that hackers can use for different nefarious actions.
“It begins with the trickery malvertising marketing campaign, continues with a artful novel solution to side-load the actual malicious code with out anybody noticing (till now!), and at last with stealing not solely your searches and shopping information, but in addition affiliation to 10,000 focused websites — a functionality that’s simply leveraged for focused spear phishing, account takeover and credential extraction — all utilizing this highly effective community of thousands and thousands of contaminated computer systems worldwide!”
All 30 of the recognized extensions work in Chrome and Edge. They could possibly be present in Google’s and Microsoft’s repositories, however each corporations eliminated most entries they confirmed malicious. Nevertheless, that does nothing for many who nonetheless have them put in. Additionally, for the reason that extensions’ code solely serves as a ruse, the apps can simply be rebranded and uploaded with one other account.
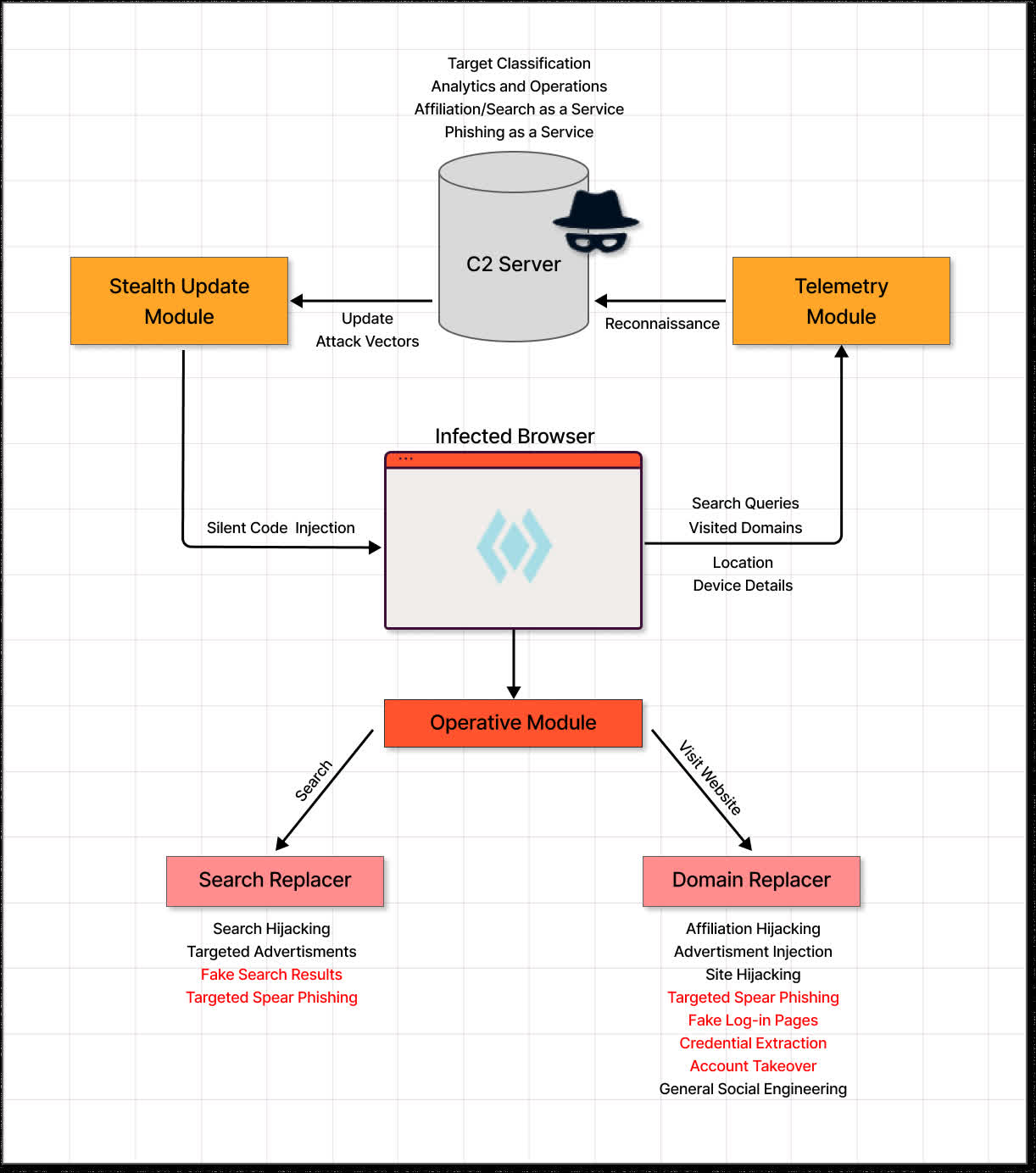
Guardio stated the software program’s nature permits attackers to focus on particular person customers or complete domains utilizing pretend search outcomes, web site hijacking, and focused spear phishing. It does this by stealing a person’s browser information and sending it to a command-and-control server. The hackers can use that information to replace the extension with new assault vectors utilizing “silent code injection.”
Usually, Google and Microsoft moderators can spot clearly malicious code and reject it earlier than it will get accredited. Nevertheless, the researchers discovered that the malware operators design the extensions in a style that enables it via inspection.
“In its preliminary state, the extension is innocent. Wanting via the code will reveal tons of colour and style-related features with names likecssbgcolors()and setlightmodes(),” Guardio says.
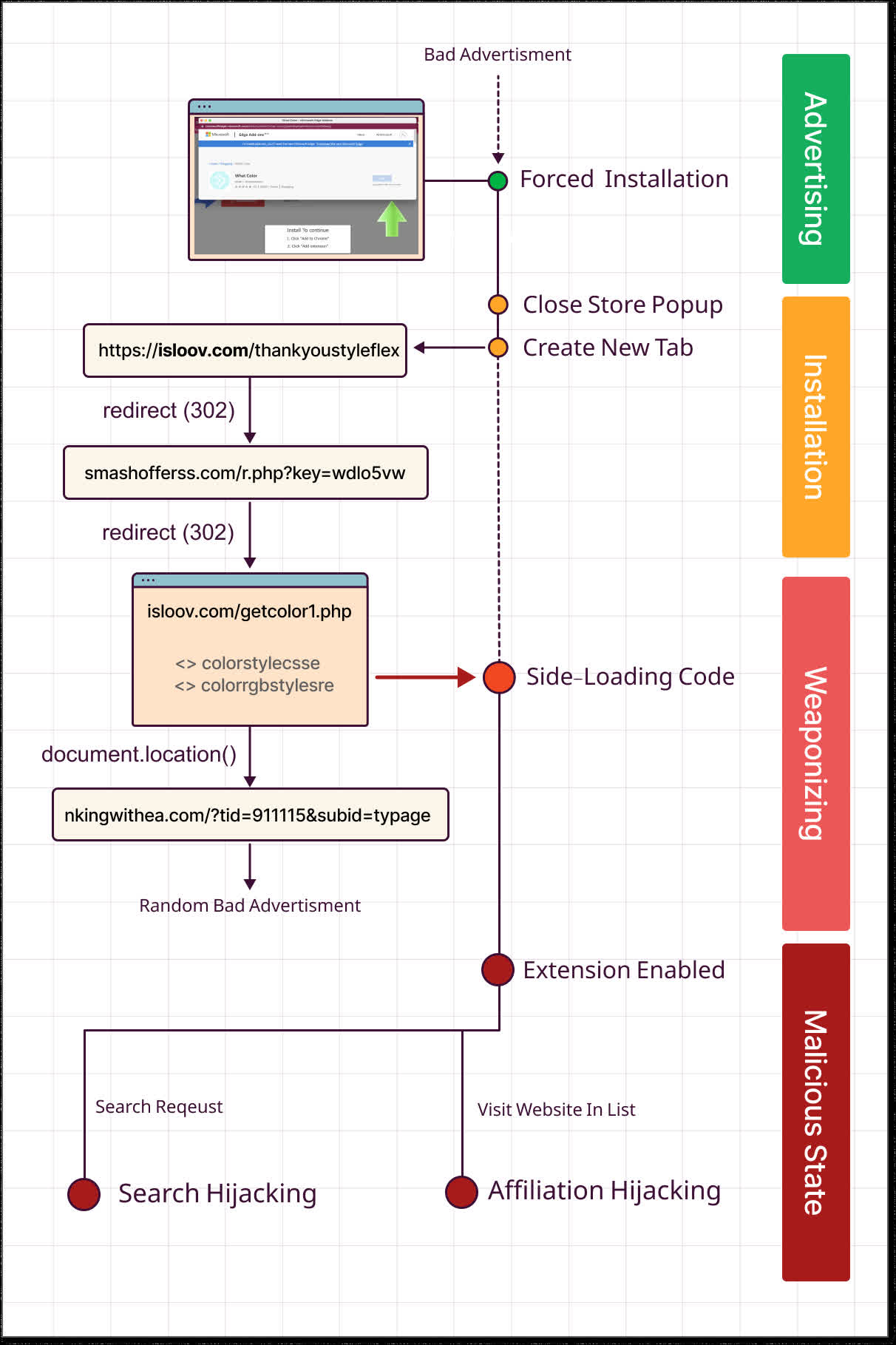
No obvious malicious code is current in what’s submitted to the shop. The difficulty comes from pretend internet pages that immediate customers to put in the seemingly innocent extension from the authentic storefront. The person is then redirected to a “thanks” web page and a collection of different redirects aspect load the malware.
The lesson right here is to rigorously take into account what extensions you select to put in in your browsers. Even when they arrive from a trusted supply, they is probably not what you count on. And particularly stay skeptical anytime a webpage tells you it’s essential to obtain something to view its content material. That may be a clear indication one thing is unsuitable and it’s astonishing that folks nonetheless fall for this trick in 2022.
In case you have any webpage styling extensions put in on Chrome or Edge, you may wish to take a look at Guardio’s totally detailed writeup.